How to Build a Dynamic Zero-Trust Network Simulation with Graph-Based Micro-Segmentation, Adaptive Policy Engine, and Insider Threat Detection
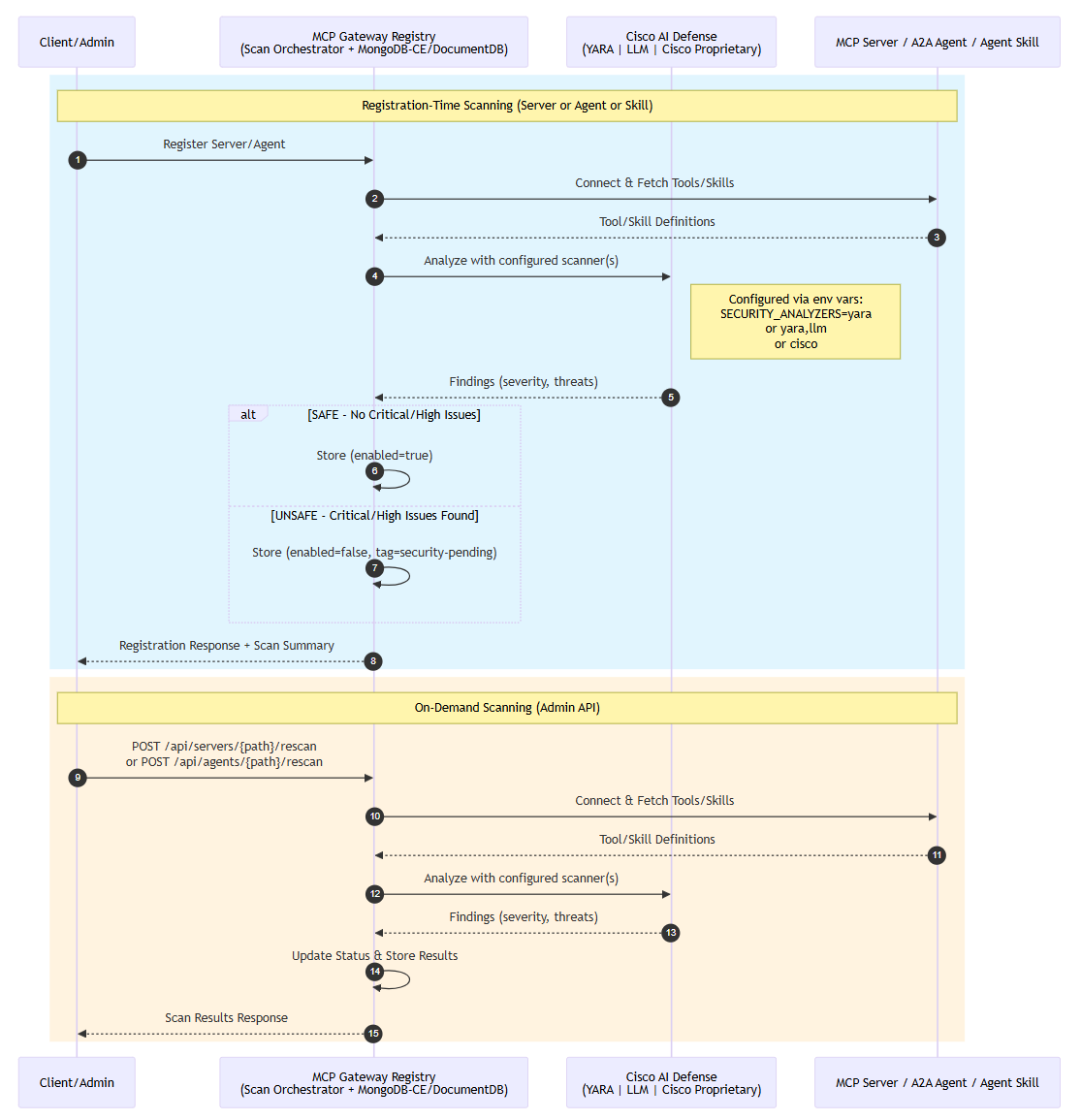
A new tutorial details how to construct a dynamic Zero-Trust network simulation using graph-based micro-segmentation and an adaptive policy engine. The method models network segments as a directed graph, requiring continuous verification for all requests. This system incorporates device posture, multi-factor authentication, and real-time risk signals to detect and block malicious activities, including insider threats, in real time. AI
IMPACT Provides a technical blueprint for enhancing network security through advanced simulation and threat detection techniques.